School of Computer and Communication Sciences

School of Computer and Communication Sciences

We take pride in educating students at all levels in the exciting and world-changing fields of science and technology, performing research that drives forward the boundaries of knowledge, as well as fostering the commercial use of our research and the entrepreneurial spirit of our faculty and students.
The artifacts and software of the technology revolution have changed peoples’ lives in countless ways over the past half century. And, this revolution is not over! The intellectual accomplishments of computer science are diffusing into many other disciplines, changing the way that researchers, practitioners, and people in general see their world and conceive of solutions. We are proud and happy to be at the center of these revolutions.


Education
We offer a bachelor program in Computer Science and one in Communications. We also offer four master’s programs: Computer Science, Communications, Data Science and Cyber Security.

Research
Research in IC spans a broad range of topics. Our faculty members are world leaders in many of these areas, and our PhD students go on to successful careers in academia and industry throughout Switzerland and the world.

Innovation
Our school works closely with industry, both in Switzerland and throughout the world, to lend our expertise to solve challenging problems and to bring new ideas from our labs into innovative products.
What’s new?

Mathieu Salzmann has officially joined the SDSC as the new Deputy Chief Data Scientist. Mathieu will co-lead a team of more than 40 researchers with postdoctoral level expertise in data science, machine learning, and AI.
23.04.24
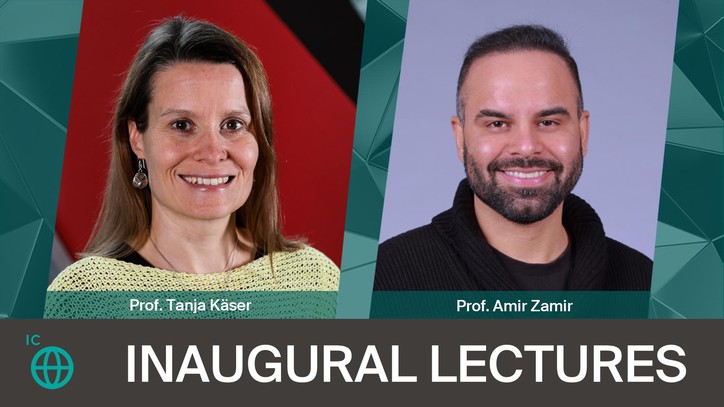
INAUGURAL LECTURES with Prof. Tanja Käser and Prof. Amir Zamir, from 6.00 pm to 7.30 pm in CE 1 4.
Contact
School of Computer and Communication Sciences
Reception
EPFL IC SG-IN
INM 168 (INM Building)
Station 14
CH-1015 Lausanne
Tel : 41 21 693 52 23
Media
EPFL IC-DO
Tel : 41 21 693 81 29
Mediacom : 41 21 693 22 22
EPFL IC-IT
Tel : 41 21 693 70 78
[email protected]



